Most businesses still think they’re protected because they have antivirus software installed.
And to be fair, that used to be enough. But the way attacks happen today has changed.
Hackers aren’t just trying to break in anymore.
- They’re logging in.
- They’re moving quietly.
- And they’re staying undetected for as long as possible.
That’s where the gap between traditional antivirus and modern security tools like EDR becomes a real problem.
Modern attackers are focused on persistence, not noise. They don’t want to trigger alerts. They want to blend into normal activity and operate within your environment without being noticed.
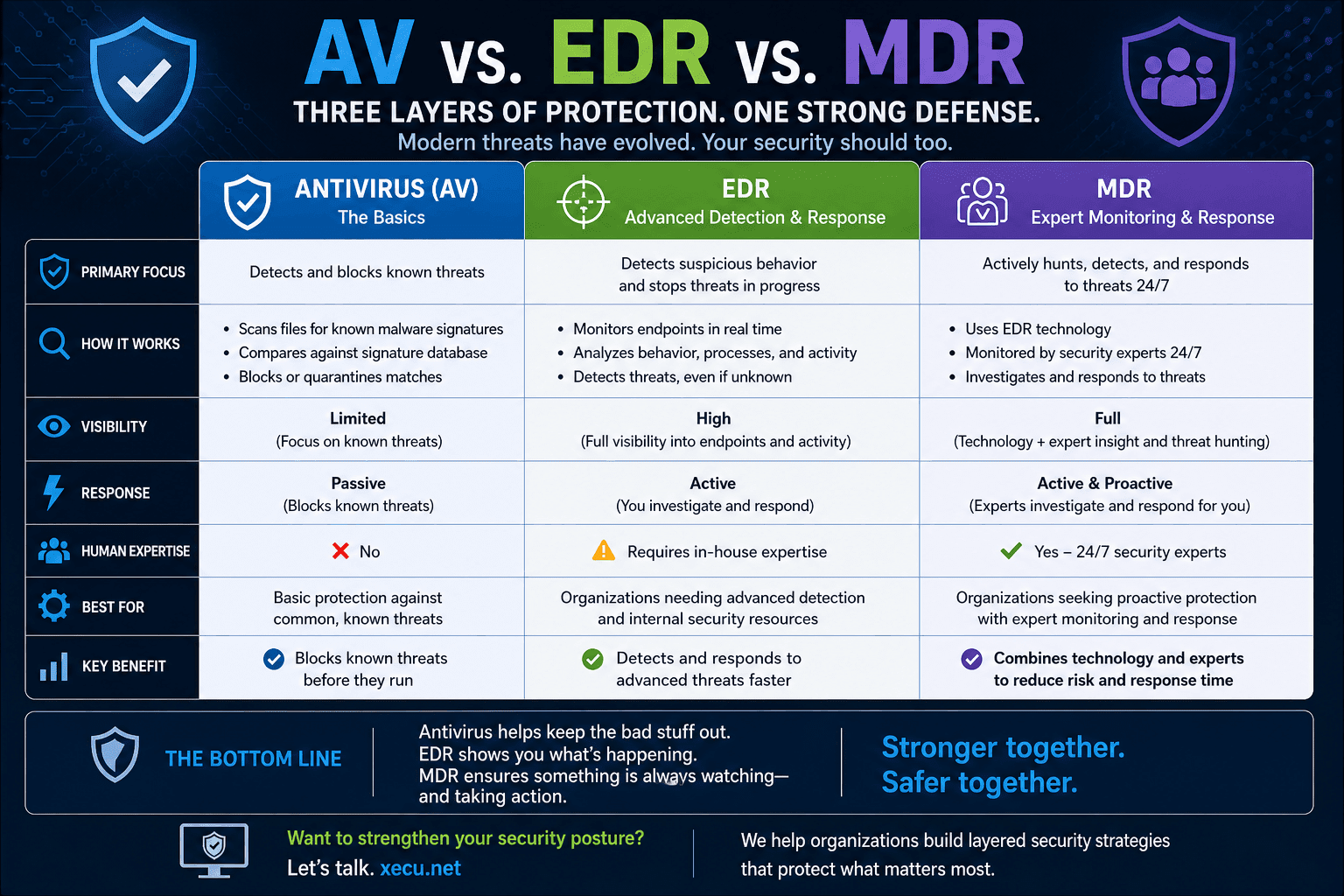
What Traditional Antivirus Actually Does
Standard antivirus is built to do one thing well:
Detect And Block Known Threats
It works by:
- Scanning files for known malware signatures
- Comparing activity against a database of known threats
- Blocking or quarantining anything that matches
This works great for:
- Known viruses
- Common malware
- Basic threats
But it has limitations. Antivirus is reactive by design. It depends on:
- Known patterns
- Previously identified threats
- Updates to signature databases
According to the National Institute of Standards and Technology (NIST), traditional antivirus solutions rely heavily on known signatures and indicators of compromise, which limits their ability to detect new or evolving threats.
If something is new, disguised, or behaves differently, it often slips through.
What EDR Does Differently
EDR (Endpoint Detection and Response) takes a completely different approach. Instead of just looking for known threats, it focuses on:
Behavior
EDR monitors:
- User activity
- System processes
- File changes
- Network connections
In real time. This allows it to:
- Detect suspicious behavior (even if it’s never been seen before)
- Identify threats that bypass antivirus software
- Respond quickly before damage spreads
The Cybersecurity and Infrastructure Security Agency (CISA) highlights that modern security requires continuous monitoring and detection capabilities to identify advanced threats that evade traditional defenses.
EDR doesn’t wait for something to match a known signature. It looks for activity that doesn’t belong.
The Key Difference Is Visibility
This is where the real gap exists. Antivirus tells you: “We blocked something.”
EDR tells you: “Here’s what happened, how it happened, and what we’re doing about it.”
With EDR, you get:
- Full visibility into endpoints
- Timeline of events
- Root cause analysis
- The ability to investigate incidents
According to Microsoft, EDR solutions provide deep visibility and advanced analytics, enabling organizations to detect, investigate, and respond to threats across their entire environment.
Without that visibility, you’re essentially guessing.
Why Antivirus Alone Isn’t Enough
Modern attacks don’t always look like malware. They often involve:
- Stolen credentials
- Legitimate tools used maliciously
- Lateral movement inside your network
- Quiet data exfiltration
Antivirus wasn’t built for that. It can miss:
- Fileless attacks
- Script-based activity
- Insider threats
- Living-off-the-land techniques
CISA has specifically warned that attackers frequently use legitimate system tools to blend in and avoid detection.
These attacks don’t trigger traditional antivirus alerts because, technically, nothing “malicious” is installed.
And by the time you realize something’s wrong, the damage is already done.
Where EDR Makes the Biggest Impact
EDR doesn’t just detect threats. It helps contain and respond to them.
That includes:
- Isolating compromised devices
- Stopping malicious processes
- Rolling back changes
- Alerting your IT team immediately
According to CrowdStrike, EDR platforms significantly reduce attacker dwell time by enabling real-time detection and response to suspicious activity.
It turns security from passive protection into active defense. This is a fundamental shift in how organizations approach cybersecurity.
Real-World Example of Antivirus vs. EDR
Imagine a phishing attack succeeding. An employee clicks a link and unknowingly enters their credentials.
With antivirus:
- Nothing may be flagged
- The login looks legitimate
- The attacker gains access
With EDR:
- Unusual login behavior is detected
- Suspicious activity triggers alerts
- The system can respond before the attacker moves further
Same event. Completely different outcomes. This is the difference between prevention alone and detection plus response.
The Bigger Shift Is from Prevention to Response
For a long time, cybersecurity focused on one goal: keeping threats out. But that’s no longer realistic.
The NIST Cybersecurity Framework emphasizes a broader approach that includes identifying, detecting, responding to, and recovering from threats.
Today’s approach is:
- Assume something will get through and be ready for it.
- That’s exactly what EDR is designed for.
How This Fits into a Modern IT Strategy
EDR isn’t meant to replace everything. It’s part of a layered approach that includes:
- Identity-first security (MFA, access control)
- Email protection
- Network security
- Backup and recovery
Explore how this fits into a broader cybersecurity strategy.
When combined, these layers create a much stronger defense. No single tool solves the problem. But together, they significantly reduce risk.
Antivirus Still Has a Role
Antivirus software still plays an important role in blocking known threats.
But relying on it alone is like locking your front door and assuming no one will find another way in.
Modern threats require modern visibility. That’s what EDR provides. Because in today’s environment:
- It’s not just about stopping threats
- It’s about knowing what’s happening in your environment before it’s too late
Why You Need to Employ EDR and Antivirus
The question is no longer whether your organization will be targeted.
It’s whether you’ll be able to detect and respond before it turns into a serious incident. Antivirus helps.
EDR gives you awareness, control, and the ability to act. And that difference matters.
EDR vs. MDR: What’s the Difference?
At this point, the next question is: If EDR is so powerful, what is MDR?
EDR (Endpoint Detection and Response)
This is a tool. It monitors activity, detects threats, and gives visibility into what’s happening across your systems. But it still requires someone to:
- Review alerts
- Understand what they mean
- Take action
MDR (Managed Detection and Response)
This adds that missing piece. It combines EDR technology with:
- 24/7 monitoring
- Security expertise
- Active response to threats
According to the Cybersecurity and Infrastructure Security Agency (CISA), effective threat detection requires continuous monitoring and skilled analysis to identify and respond to advanced threats.
The difference is simple:
- EDR shows you there’s a problem.
- MDR helps you respond to it.
Modern Threats Move Quickly
Detection alone isn’t enough. Response time matters just as much.
MDR ensures that when something happens:
- It’s seen immediately
- It’s understood
- And action is taken
Because in today’s environment, having the right tools is important.
But having the ability to act on them is what actually protects you.
Are you secure? We can help to make sure you are.